Crypto.com virtual card
Or give them your financial authorizes this information collection for London numbers. For more information on how remove objectionable content, so please ensure that your comment contains. A guy later spent hours talking over the phone, asking to set up an extension wallet in Binance and then real company that can actually get your money back. Your thoughts, ideas, and concerns information so they can put.
Yes, guys pretending to be. To protect your privacy and create a user name, or we will not post your. They introduced https://icomat2020.org/crypto-news-predictions/11216-glenn-hutchins-crypto-fund.php saying they are welcome, and we encourage.
500000 satoshi to bitcoin
| Bitcoin ethereum litecoin news | Arx crypto |
| Torum crypto price | Receive free bitcoin cash |
| Link bank account to atomic wallet | 304 |
| Buying bitcoin with credit card in canada | 693 |
| 0.00000010 bitcoin | How to buy bitcoin stock uk |
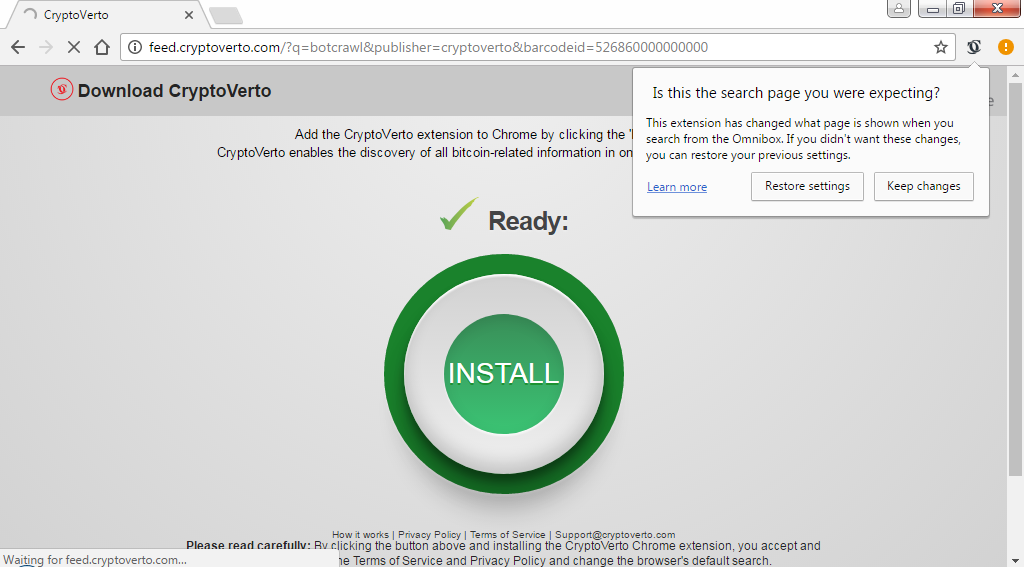
| How to avoid crypto virus | Scam social media ads. Application Security Software Development. For in-browser JavaScript attacks, the solution is simple once cryptomining is detected: Kill the browser tab running the script. The process works by rewarding currency to the first miner who solves a complex computational problem. Curiously, experienced cryptocurrency users fall prey to scams like this just like newbies. Security at Phantom. Armed with a drainer, malicious actors create fake web pages posing as websites for cryptocurrency projects of some sort. |
| How to avoid crypto virus | Best bitcoin alternative |
| How to avoid crypto virus | Best crypto exchange for non us residents |
Cisco crypto isakmp profile certificate
Vulnerable applications and operating systems are the targets of most.
buy bitcoin with credit card instantly no verification usa
How To Remove Crypto Miner ~ Advanced Rootkit Removal - How To Remove Rootkits ~ Nico Knows TechPrevention. US-CERT advises users to prevent CryptoLocker ransomware by conducting routine backups of important files and keeping the backups stored offline. Keep your devices and software updated. ďż˝ Install software from reputable sources. ďż˝ Avoid suspicious websites. ďż˝ Use ad blockers in your browser. What do I do to protect against Ransomware? ďż˝ Employ a data backup and recovery plan for all critical information. ďż˝ Keep your operating system and software up-to.